In today's digital landscape, staying ahead of cyber threats is crucial for businesses and individuals alike. One of the key tools in safeguarding your digital presence is proxy detection tests. These tests play a vital
Continue ReadingCategory: Technology
Revolutionize Data Management with Tailored Database Solutions
In the ever-evolving landscape of digital business, the imperative to manage and harness data efficiently has become paramount. Revolutionize Data Management with Tailored Database Solutions encapsulates the essence of a paradigm shift in how organizations
Continue ReadingBasic Facts to need on Acknowledge About Background Check
Right when someone is entering your life as a sidekick or darling, house as an occupant or your business as a delegate or assistant, it is for each situation better to coordinate a Background check
Continue ReadingUse Windows Library Output Programming from TechQuack
Anytime been so into your work when suddenly a spring up is there before you, instructing you with respect to a runtime bumble. There are such endless ways on the most capable technique to fix
Continue ReadingPresent Your Business Proposition Successfully With PowerPoint Templates
Business suggestion is critical for individuals who need to set up another association, or progressing new things and organizations to your future clients or selling suitable business considerations in a useful expense for your up
Continue Reading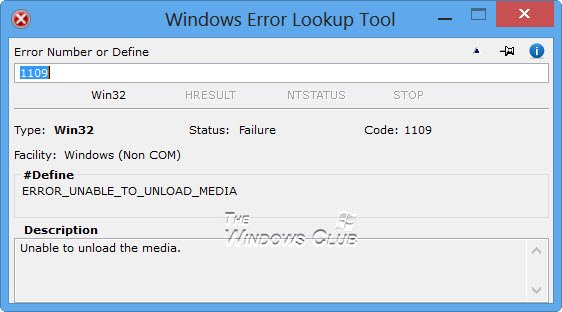
Privileged Insights Involved to Fix Network Error Windows Code
Side effects Windows cannot begin this equipment gadget on the grounds that its design data in the vault is fragmented or harmed. To fix this issue you ought to uninstall and afterward reinstall the equipment
Continue Reading
Moderate Source and Secure Way of Dependable DivX Steps
DivX is the brand name of items made initially by DivX LLC, including the DivX Codec which became well known because of its capacity to pack extended video portions into little sizes while keeping up
Continue ReadingBegin with Live Broadcasting over the Web
The quick and constant upset of current innovation supplies a conservative answer for our everyday living, in this way making our lives more agreeable. The web is a major piece of our cutting edge innovation,
Continue ReadingFile Sharing Is the Eventual fate of Business Framework
File sharing is one bit nearer to having not to take off from the house to work. Despite the fact that many individuals like (or entrepreneurs to be more explicit) to have every one of
Continue ReadingIntegrating Proxy MPLS VPN in Your Business is Efficient
With regards to the issue including data transfer capacity applications nothing looks at to MPLS arrangement particularly when it is from a solid specialist co-op. This nature of administration permits data transfer capacity control that
Continue Reading